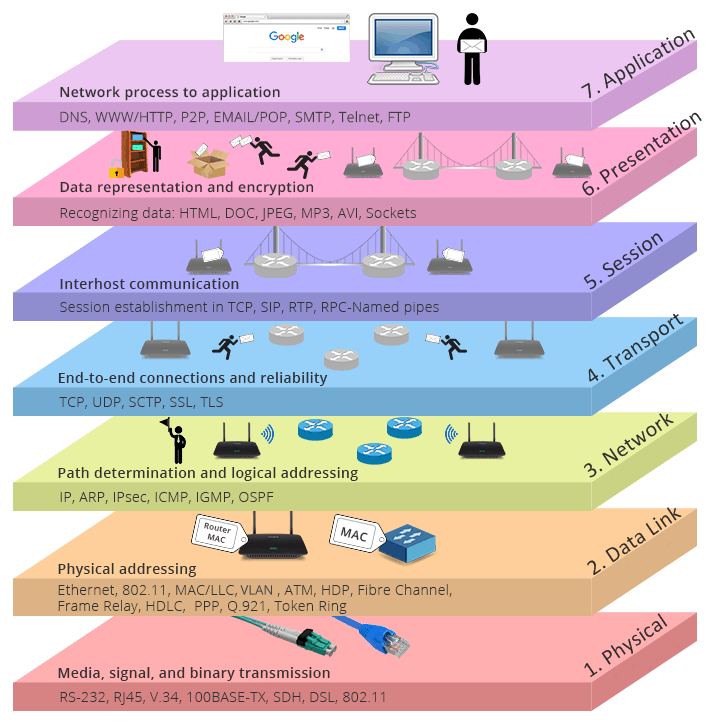
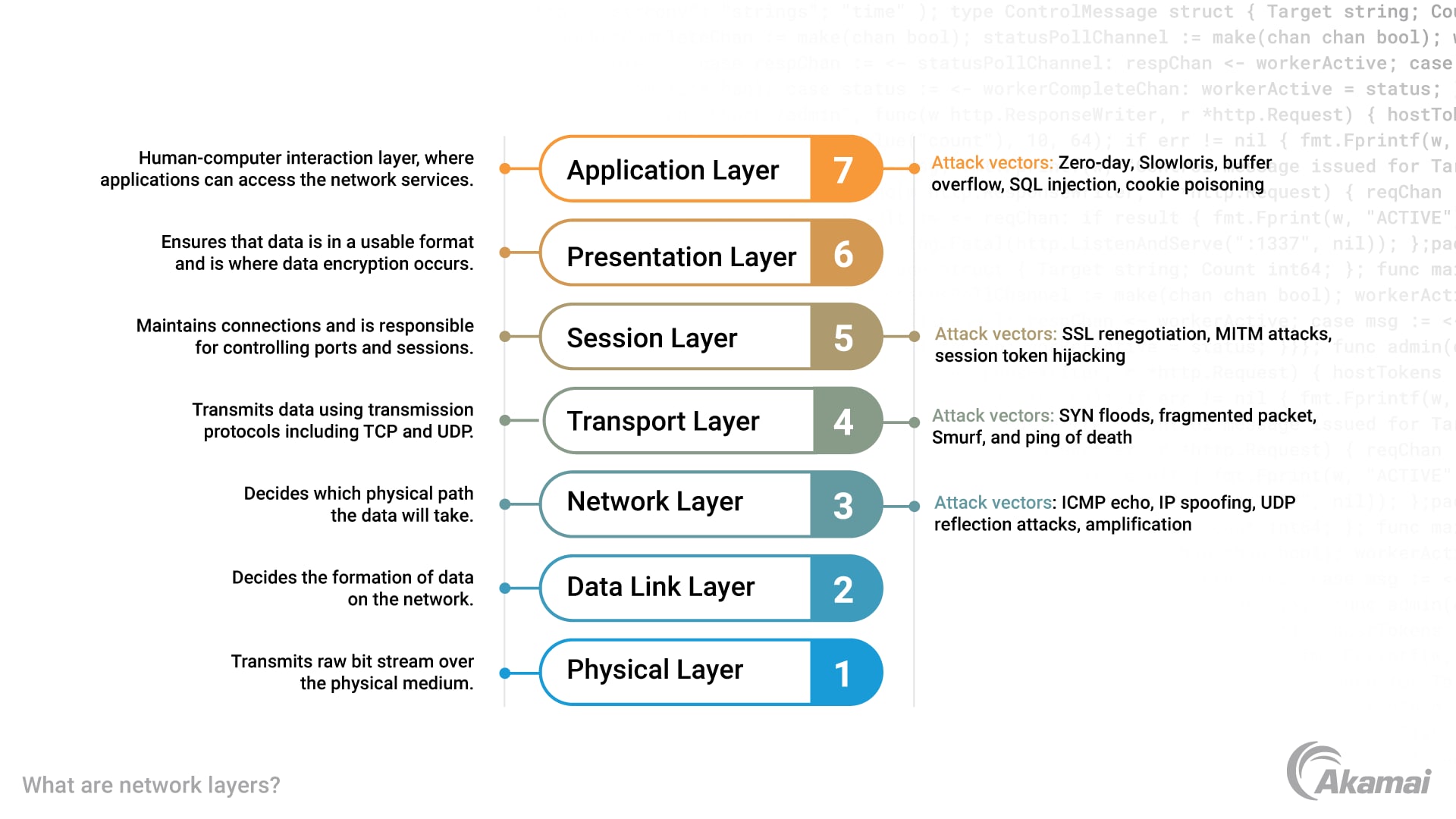
Learn Linux with Dan | ✓ Cybersecurity threats in OSI model . Security attackers can exploit vulnerabilities in any of the existing network layers, from physi... | Instagram

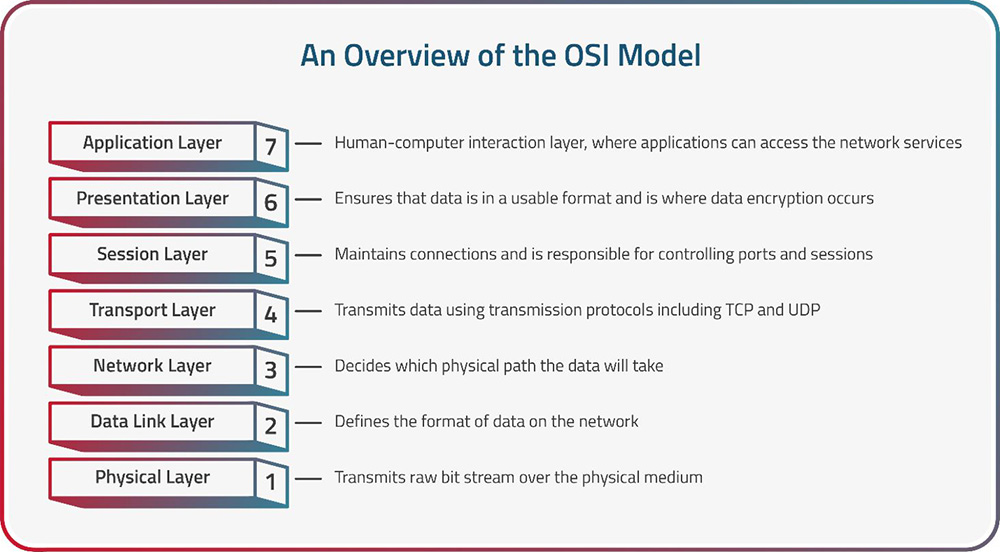
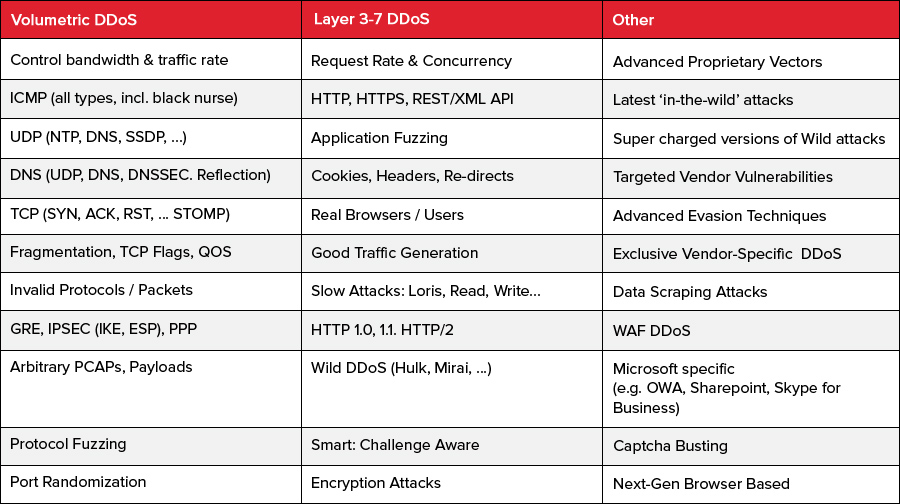
Security Trybe on X: "OSI Layers and Attacks #cyberattacks #CyberSec #infosec #cybersecurity #Hacking #Hacked https://t.co/6lEcLSQtJu" / X







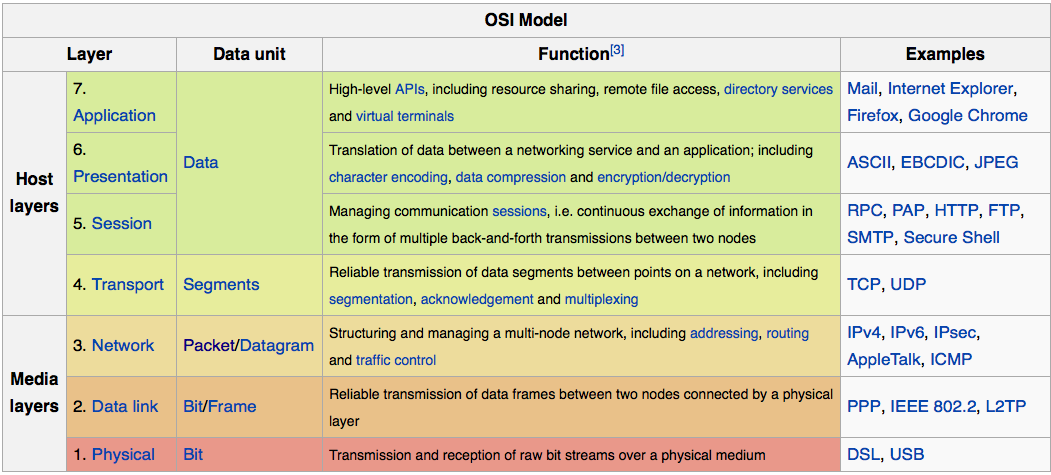


.png)